Hyperjacking
| This article is part of a series on |
| Computer hacking |
|---|
| History |
| Hacker ethic |
| Conferences |
| Computer crime |
| Hacking tools |
| Practice sites |
| Malware |
| Computer security |
| Groups |
Hyperjacking is an attack in which a hacker takes malicious control over the hypervisor that creates the virtual environment within a virtual machine (VM) host.[1] The point of the attack is to target the operating system that is below that of the virtual machines so that the attacker's program can run and the applications on the VMs above it will be completely oblivious to its presence.
Overview
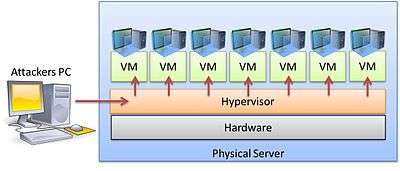
Hyperjacking involves installing a malicious, fake hypervisor that can manage the entire server system. Regular security measures are ineffective because the operating system will not be aware that the machine has been compromised. In hyperjacking, the hypervisor specifically operates in stealth mode and runs beneath the machine, it makes more difficult to detect and more likely gain access to computer servers where it can affect the operation of the entire institution or company. If the hacker gains access to the hypervisor, everything that is connected to that server can be manipulated.[2] The hypervisor represents a single point of failure when it comes to the security and protection of sensitive information.[3]
For a hyperjacking attack to succeed, an attacker would have to take control of the hypervisor by the following methods:[4]
- Injecting a rogue hypervisor beneath the original hypervisor
- Directly obtaining control of the original hypervisor
- Running a rogue hypervisor on top of an existing hypervisor
Mitigation techniques
Some basic design features in a virtual environment can help mitigate the risks of hyperjacking:
- Security Management of hypervisor must be kept separate from regular traffic. This is more network related measurement than a hypervisor itself related.[1]
- Guest operating systems should never have access to the hypervisor. Management tools should not be installed or used from guest OS.[1]
- Regular patching the hypervisor.[1]
Hypervisor training can be found at How to Use a Hypervisor in Cloud Computing Virtualization, which illustrates the basics of hypervisor administration.
Known attacks
As of early 2015, there had not been any report of an actual demonstration of a successful hyperjacking besides "proof of concept" testing. The VENOM vulnerability (CVE-2015-3456) was revealed in May 2015 and had the potential to affect many datacenters.[5] Hyperjackings are rare due to the difficulty of directly accessing hypervisors; however, hyperjacking is considered a real-world threat.[6]
References
- 1 2 3 4 "HYPERJACKING". Telelink. Retrieved 27 February 2015.
- ↑ Gray, Daniel. "Hyperjacking - Future Computer Server Threat". SysChat. Retrieved 27 February 2015.
- ↑ Ryan, Sherstobitoff. "Virtualization Security - Part 2". Virtualization Journal. Retrieved 27 February 2015.
- ↑ Sugano, Alan. "Security and Server Virtualization". WindowsITPro. Retrieved 27 February 2015.
- ↑ "VENOM Vulnerability". CrowdStrike.com. Retrieved 18 October 2016.
- ↑ "Common Virtualization Vulnerabilities and How to Mitigate Risks". Penetration Testing Lab. Retrieved 27 February 2015.